 |
| https configuration |
Question : how to configure HTTP in Linux centos 6 , rhel 6
Question : step by step HTTP configuration in Linux centos6 , rhel6
Question : step by step http & https configuration in Linux cento6 , rhel6
Question : How to generate SSL Certs ?
IP - 10.20.2.33
Hostname - khandwa.lokesh.com
OS - CentOS 6
PORT HTTP - 80, HTTPs - 443
Apache is a free and opensource Web server. It s Supports all major distribution such as windows, Linux , Solaris and Mac operating system.
Some important directories are listed below
/etc/httpd - Main Apache root configuration directory.
/etc/httpd/conf.d - Additional Apache configuration files provided by third party software
/etc/httpd/conf/httpd.conf - httpd main configuration file.
/var/lib/httpd/modules - Configuration files for additional modules
/etc/log/httpd - Contains log files
/var/www - Main web document root directory.
To Install Require Package using yum or rpm
yum install http*To Restart httpd service & enable to start for every boot.
service httpd restart checkconfig httpd on
http://your_IP_address.
or
http://your _hostname.

Create Virtual Hosts :
Configure / Run several websites on the same server called a virtual hosting . Virtual hosts can be "IP-based", meaning that you have a different IP address for every web site, or "name-based", meaning that you have multiple names running on each IP address.
(*) you can set IP address of your server
NameVirtualHost *:80

Create Virtual Hosts :
Configure / Run several websites on the same server called a virtual hosting . Virtual hosts can be "IP-based", meaning that you have a different IP address for every web site, or "name-based", meaning that you have multiple names running on each IP address.
(*) you can set IP address of your server
NameVirtualHost *:80
Step 1:
Create a directory for content of website, we can choose any name and create directory :

Step 2
mkdir /var/www/html/lokesh.comCreate a index file under lokesh.com directory
vi /var/www/html/lokesh.com/index.html

Step 2
We will Create new virtual host configuration file under the additional configuration directory

Step 3
To Check Syntax Error in Apache Configuration
vi /etc/httpd/conf.d/lokesh.confGo to insert mode & type following lines
<VirtualHost 10.20.2.33:80> ServerAdmin [email protected] DocumentRoot /var/www/html/lokesh.com ServerName lokesh.com ErrorLog logs/lokesh.com-error_log CustomLog logs/lokesh.com-access_log common</VirtualHost>

Step 3
To Check Syntax Error in Apache Configuration
service httpd configtest
Basic Configuration of HTTP is almost done now we will restart httpd service,

HTTPs Configuration | Apache Security | HTTPs
Install Require Package Using yum
A cryptographic protocol that allows a server and a client to communicate securely called Secure Sockets Layer (SSL). Along with its extended and improved version called Transport Layer Security (TLS), it ensures both privacy and data integrity.
service httpd restart

HTTPs Configuration | Apache Security | HTTPs
Install Require Package Using yum
yum install opensslyum install mod_ssl Or mod_nss ( only one of them)Setting Up an SSL Server:
A cryptographic protocol that allows a server and a client to communicate securely called Secure Sockets Layer (SSL). Along with its extended and improved version called Transport Layer Security (TLS), it ensures both privacy and data integrity.
The Apache HTTP Server in combination with mod_ssl, a module that uses the OpenSSL toolkit to provide the SSL/TLS support, is commonly referred to as the SSL server.
Enabling / Disabling SSL and TLS

To Restart httpd service
Enabling / Disabling SSL and TLS
vi /etc/httpd/conf.d/ssl.confEdit the SSLProtocol line as follows

To Restart httpd service
service httpd restartTest SSL / TLS Protocols
openssl s_client -connect localhost:443 -ssl3

Check https listen port in : etc/httpd/conf.d/ssl.conf. it should always enable with 443 port
Listen: 443
Generating SSL Certificate
Method 1
To install crypto utility
yum install crypto-utilsTo run the utility:
genkey <hostname>genkey khandwa.lokesh.comReview the target locations in which the key and certificate will be stored

Select "Next" Using the up and down arrow keys,
Now select a suitable key size

Press "Next"
Generate CSR = Yes
encrypt the private key = check & hit enter
set private key passphrase = choose pass & next
Enter your certificate detail

Press "Next" & then "Finish"
Generate CSR

Copy files to the correct locations

Note - If you have moved the files and not copied them, you can use the following command to correct the SELinux contexts on those files, as the correct context definitions for /etc/pki/* come with the bundled SELinux policy.
Now Create Virtual Hosts for HTTPs with same process like http.
<VirtualHost *:443>

Press "Next"
Generate CSR = Yes
encrypt the private key = check & hit enter
set private key passphrase = choose pass & next
Enter your certificate detail

Press "Next" & then "Finish"
Method 2
Generate a self-signed certificate : Generate private keyopenssl genrsa -out ca.key 2048Here ca.key is a key name & 2048 is key size.
Generate CSR
openssl req -new -key ca.key -out ca.csrGenerate Self Signed Key
openssl x509 -req -days 365 -in ca.csr -signkey ca.key -out ca.crt

Copy files to the correct locations
cp ca.crt /etc/pki/tls/certscp ca.key /etc/pki/tls/private/ca.keycp ca.csr /etc/pki/tls/private/ca.csr

Note - If you have moved the files and not copied them, you can use the following command to correct the SELinux contexts on those files, as the correct context definitions for /etc/pki/* come with the bundled SELinux policy.
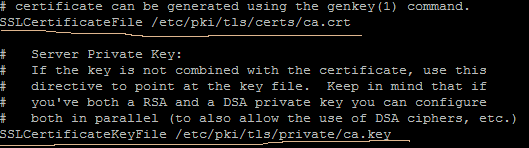
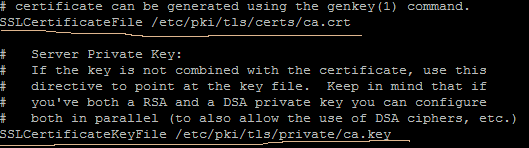
restorecon -RvF /etc/pkiAdd certs file in Apache Configuration
vi +/SSLCertificateFile /etc/httpd/conf.d/ssl.conf
Now Create Virtual Hosts for HTTPs with same process like http.
mkdir /var/www/html/khandwa.lokesh.com
vi /var/www/html/khandwa.lokesh.com/index.htmlConfigure VirtualHost
vi /etc/httpd/conf.d/khandwa.lokesh.conf
<VirtualHost *:443>
SSLEngine on
SSLCertificateFile /etc/pki/tls/certs/ca.crt
SSLCertificateKeyFile /etc/pki/tls/private/ca.key
<Directory /var/www/html>
AllowOverride All
< /Directory>
DocumentRoot /var/www/html
ServerName khandwa.lokesh.com
ServerAdmin [email protected]
ErrorLog logs/khandwa.lokesh.com-error_log
CustomLog logs/khandwa.lokesh.com-access_log common
</VirtualHost>

Restart and enable httpd Service
Service httpd restart
Chkconfig httpd on
Access secure web server on blow link
https://khandwa.lokesh.com


